- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
QlikView and SAML with OneLogin
SAML is not supported by default in QlikView but can be implemented by creating a custom authentication module that will convert SAML requests/responses to QlikView Ticket to log the user in.
This customization is provided as is. Qlik Support cannot provide continued support of the solution. For assistance, contact our Professional Services or engage in our QlikView Integrations forum.
Currently, this solution only works for SP initiated authentication. Making it work for IDP-initiated authentication might require further code changes in the library/module source code.
This has been tested with QlikView 12.10 SR7.
Requirements:
- IIS installed with asp .net development language
- .NET framework 4.0
- Copy and unzip qvsaml.zip in the root of your IIS website. Make sure to edit the bindings of your website and set up https.
Configuration on the QlikView side:
- Edit the file C:\ProgramData\QlikTech\WebServer\config.xml to include the IP address of the machine where the authentication module is hosted.
You will need to change the line:
to<GetWebTicket url="/QvAjaxZfc/GetWebTicket.aspx"/><GetWebTicket url="/QvAjaxZfc/GetWebTicket.aspx"> <TrustedIP>fe80::b178:730a:5c2a:86d2%11</TrustedIP> </GetWebTicket> - If you are unsure if the request is sent over IPv4 or IPv6, you can just use: ping servername in a command prompt and see which IP address is returned.
Configuration of the authentication module:
- Copy your authentication module code in your IIS site folder. The site needs to be run over HTTPS.
The sample is built using "CodeBehind" so you will need to compile the source code and place the compiled binary in the bin folder for the sample to work.
A compiled version "QlikViewSamlAuthentication.dll" is provided as is.
The sample also uses the third party library OIOSAML.NET (version 2.0.1): https://www.digitaliser.dk/resource/3868871
A compiled version that works with OneLogin (dk.nita.saml20.dll) is provided as is.
If you choose to compile the source code yourself for use with OneLogin, you will need to comment out the statement to check that the name is an URI as this attribute is an email address in OneLogin:
File: DKSaml20AttributeValidator.cs - Before:
public void ValidateAttribute(SamlAttribute samlAttribute) { if (!Uri.IsWellFormedUriString(samlAttribute.Name, UriKind.Absolute)) throw new DKSaml20FormatException("The DK-SAML 2.0 profile requires that an attribute's \"Name\" is an URI.");after
public void ValidateAttribute(SamlAttribute samlAttribute) { /* if (!Uri.IsWellFormedUriString(samlAttribute.Name, UriKind.Absolute)) throw new DKSaml20FormatException("The DK-SAML 2.0 profile requires that an attribute's \"Name\" is an URI."); */ - Settings for QlikView in the module web.config:
Replace https://qlikserver1.domain.local/ by your qlikview server URL in the above code.<QlikViewSaml accessPointUrl="https://qlikserver1.domain.local/" authenticatePage="QvAjaxZfc/Authenticate.aspx" webTicketPage="QvAjaxZfc/GetWebTicket.aspx" tryPage="https://qlikserver1.domain.local/qlikview/" backUrl="https://qlikserver1.domain.local/webticketerror.html" /> - Settings for the Audience:
<AllowedAudienceUris> <Audience>https://qlikserver1.domain.local</Audience> </AllowedAudienceUris>
*It must exactly match the setting you have in Onelogin. - Settings for the certificate used to sign the SAML request:
*In this case, we use a certificate that has "CN=qlikserver1" as its distinguished name.<Federation xmlns="urn:dk.nita.saml20.configuration"> <SigningCertificate findValue="CN=qlikserver1" storeLocation="LocalMachine" storeName="My" x509FindType="FindBySubjectDistinguishedName"/>
*You need to install the certificate in Windows first. It must have a private key. - Settings for the folder for the IDP metadata:
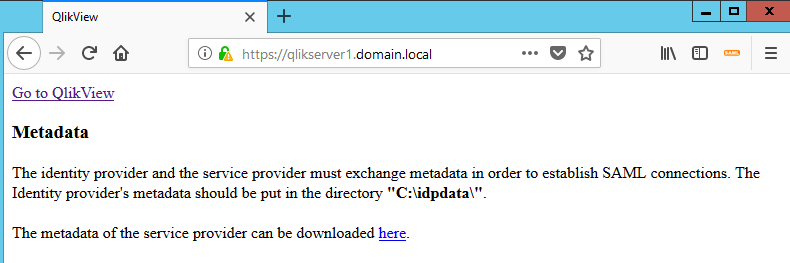
<IDPEndPoints metadata="C:\idpdata\"> ...
*In this example, the folder is C:\idpdata, once Onelogin is set up, download the metadata from Onelogin and copy it in this folder.
Configuration of OneLogin
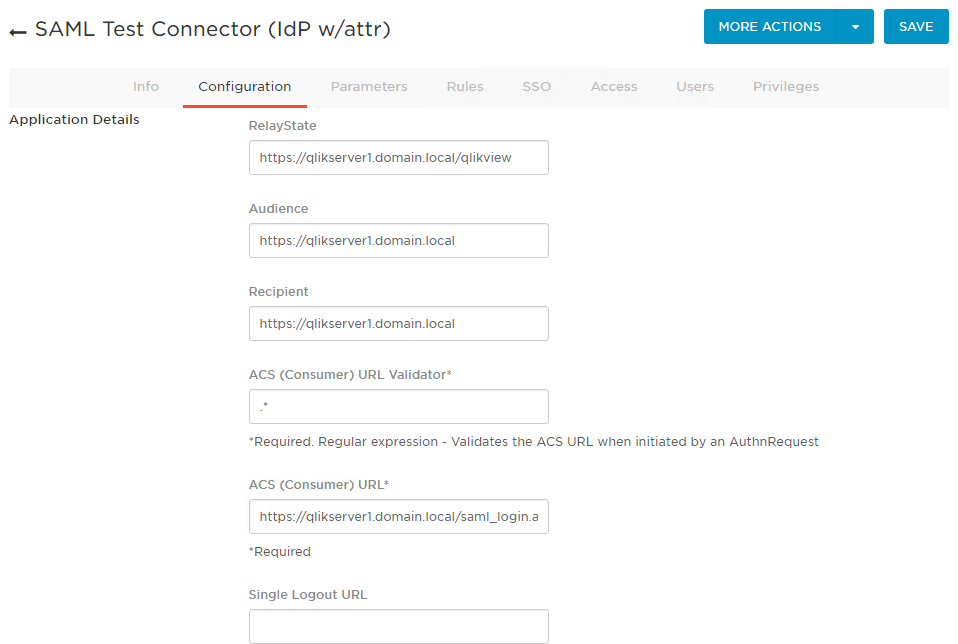
- Create a new company app using the template "SAML Test Connector (IdP w/attr)". Below, you can find the settings used in this example:
- Make sure that the audience set here matches what you have in the web.config of the module
- In saml_login.aspx (file that handles the SAML request in the module), make sure the URL is correct.
Other tabs are left at default values.
Test the solution and log in:
- Open the URL of your module (In this case, the module is hosted in IIS on the same server as QlikView):
- Click on "Go to QlikView" and you should get to the Onelogin login page:
- Once you're logged in, you should be redirected to the Access point, notice your user name in the upper right corner:
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
This is with OneLogin. Do we need to compile the code again for QlikView April2020? We already have this custom solution working on 12.10.20200 version but when we tried on April 2020, its not working.
Our IDP is Microsoft Azure (MyApps).
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi @Damien_V ,
Are there any documentions or KB on SAML integration when the QV is hosted on the QVWS server and not IIS?
Thanks
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @ilyas393
IIS is a requirement, as the QlikView Webserver itself does not allow for the customization needed. If you require custom solutions, I would recommend reaching out to our professional services for further assistance.
All the best,
Sonja
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @Damien_V @Sonja_Bauernfeind ,
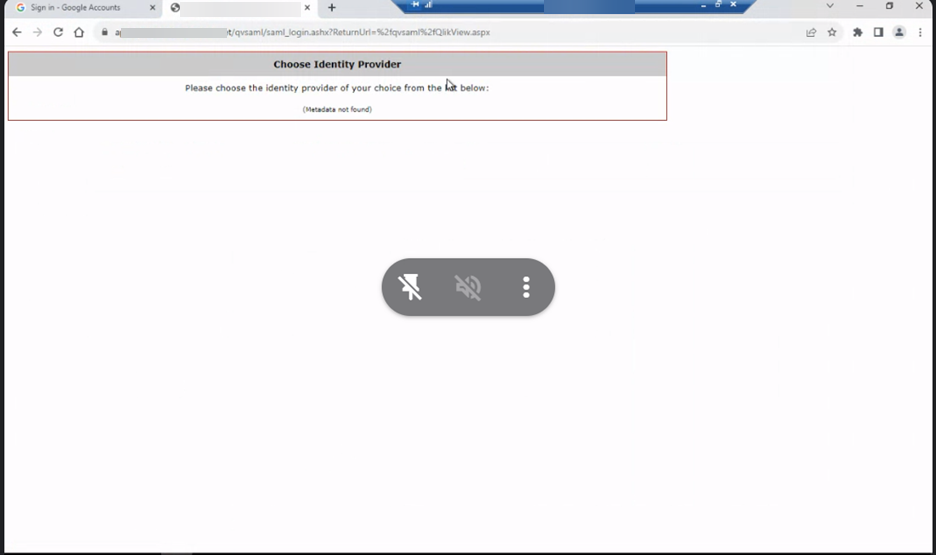
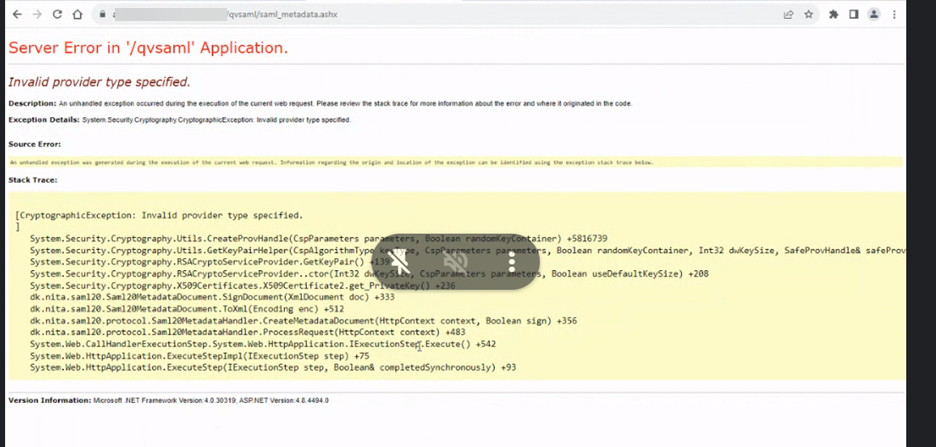
We have followed the same steps mentioned to implement SSO with Google as IdP. While "Test the solution and log in: "hile we are able to get till step 1 in it. However as soon as we click on "Go To QlikView " we are error as below. Metadata of Idp is placed in C:\idpdata\ but we don't have any SP metadata to download and upload in configuration of Google SSO. Could you please let us know what is going wrong here ?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @sanrout
This customization is provided as is. Qlik Support cannot provide continued support of the solution. For assistance, contact our Professional Services or engage in our QlikView Integrations forum.
All the best,
Sonja
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@sanrout
Were you able to get past the choose identity provider screen you posted? I am running into the same issue