Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Support
- :
- Support
- :
- Knowledge
- :
- Support Articles
- :
- Disabling Server Header
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Disabling Server Header
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Disabling Server Header
Oct 12, 2021 8:21:19 AM
Feb 4, 2019 1:42:26 PM
It is important to suppress as much information as possible from any potentially harmful user.
The server contains information identifying the technology being used and version numbers. This is not desirable because it increases the attack surface and could allow a malicious user to perform a spearheaded attack.
Environment:
QlikView
Qlik Sense Enterprise on Windows
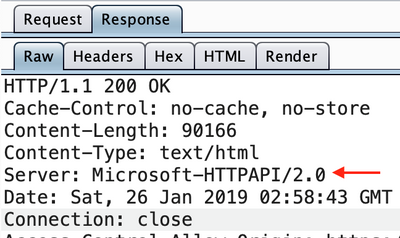
On Windows, whether that is server edition or regular, it is not very clear as to how to disable this header. These instructions aim to clarify and demonstrate how it could be done on either edition. Without disabling the header, the server gives information away regarding the technology it is utilizing, as seen below.
Resolution:
In order to stop the server from handing out information regarding the technology it is utilizing, we need to disable the “Server” header. This could be achieved in a number of ways. Instances running IIS could utilize “URLScan” or “Custom HTTP Rules”. However, this is not a universal solution and in the case of URLScan, it is required to install an add-on to IIS. As a result, the following method will only target the HTTP service which works on any version of Windows.
- Open up “regedit.exe” (Run as Administrator) and navigate to:
HKLM\System\CurrentControlSet\Services\HTTP\Parameters - Create a DWORD entry.
- Right-click on the whitespace
- New
- DWORD (32-bit) Value
- Rename the new entry to “DisableServerHeader”
- Set its value to 2
- Hit “OK”.
Creating a DWORD entry for “DisableServerHeader”
Setting the value of DisableServerHeader to 2
- In order for this to take effect, it is required to reset the “http” service.
Warning: This will make your web services relying on HTTP unresponsive.
- Open CMD (or PS) as administrator and run the following:
net stop HTTP net start HTTP - If the above method fails, reboot the system.
- Open CMD (or PS) as administrator and run the following:
- Once the service has been restarted successfully, the response header from the server should now look similar to this:
No Server Header in the HTTP response