Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Support
- :
- Support
- :
- Knowledge
- :
- Support Articles
- :
- Qlik Sense: Information needed to Troubleshoot SAM...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Qlik Sense: Information needed to Troubleshoot SAML SSO related issues
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Qlik Sense: Information needed to Troubleshoot SAML SSO related issues
May 10, 2022 3:07:45 PM
Oct 29, 2017 5:46:50 AM
Disclaimer: In Qlik Sense, SAML is a supported authentication method that can be used. However the infrastructure to make SAML works will need to be set by the customer. Please be aware that Qlik Support can not help in the setting up of SAML/SSO or related issues. If the customer needs help to set up SAML from scratch, Qlik Consulting needs to be invoked. This is out of scope for Support.
Qlik Support will do a first assessment of SAML related support cases in order to understand if the issue is related to a possible defect in the implementation of SAML in Qlik Sense or a wrong setup.
This article gathers information needed for Qlik Support to assess a SAML related support case.
Environments:
The following six pieces information are required when investigating a SAML-related issue:
- The error encountered when trying to log in. Below is an example (Fig 1).
Fig 1
- The SAML Identity provider used (ADFS, Okta, Azure, Onelogin, etc.)
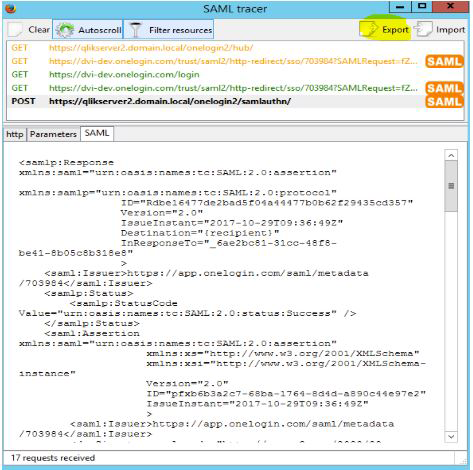
- Export of SAML trace logs
This can be collected using a browser extension such as SAML Tracer for Firefox on the client that is trying to log in using SAML. The below image highlights how/where to export SAML trace logs.
This is a very important piece of information, as without these logs it is not possible to tell what is happening when the user actually tries to authenticate!
If the SAML assertion is encrypted, copy it in https://www.samltool.com/decrypt.php and provide your private key to get the decrypted assertion to send it to Qlik Support. - The Qlik Sense Proxy logs (By default in C:/Programdata/Qlik/Sense/log/Proxy, see How To Collect Qlik Sense Log Files for the Log Collector). Note, in a multinode environment these logs will be on the node hosting the Proxy service linked to the SAML virtual proxy.
- Screenshot of how the virtual proxy for SAML has been set up in Qlik Sense
- The SAML Identity provider metadata file