Unlock a world of possibilities! Login now and discover the exclusive benefits awaiting you.
- Qlik Community
- :
- Support
- :
- Support
- :
- Knowledge
- :
- Support Articles
- :
- Mitigating against clickjacking in Qlik Sense and ...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Mitigating against clickjacking in Qlik Sense and QlikView, X-FRAME Options in response header
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mitigating against clickjacking in Qlik Sense and QlikView, X-FRAME Options in response header
Nov 14, 2022 6:09:57 AM
Jul 20, 2016 5:21:17 PM
Using a similar technique, keystrokes can also be hijacked. With a carefully crafted combination of stylesheets, iframes, and text boxes, a user can be led to believe they are typing in the password to their email or bank account, but are instead typing into an invisible frame controlled by the attacker. (source)
In Qlik Sense and QlikView, using the default setup, it is possible to embed a Qlik Sense site or a QlikView App into an iframe external to the site and, potentially, capture credentials.
The main defence against this potential vulnerability is to set the X-Frame-Options Response Headers in the requests. This governs whether a browser should or should not render a page inside an iFrame.
There are a handful of values that can be configured. The support for those dependent on the web browser, so do investigate the type of X-Frame-Option that you are setting.
Qlik Sense
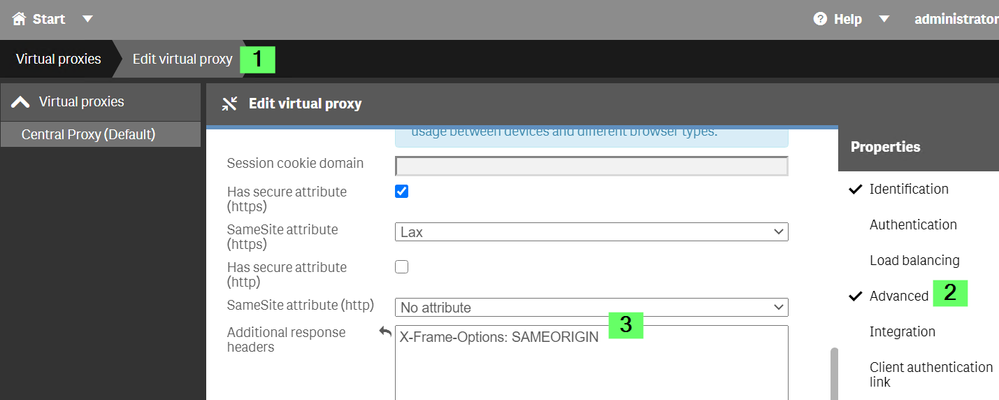
- Open the Qlik Sense Management Console
- Navigate to the Virtual Proxy used in the implementation
- Click Edit
- Select Advanced in the right-hand side menu
- Locate Additional response headers
- Add: X-Frame-Options: SAMEORIGIN
QlikView
QlikView allows for the use of custom headers (much like Qlik Sense) natively beginning with the 12.30 release.
See QlikView WebServer: Custom HTTP Header.
You can also implement them using IIS if IIS is being used as the web server: Setting Custom HTTP Headers in IIS for QlikView.
Related Content
How to allow Qlik Sense to be embedding in an iFrame only from specific websites
Environment
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
is there any of the same reference to mitigate against clickjacking in qlikview?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @Luck
QlikView allows for the use of custom headers (much like Qlik Sense) natively beginning with the 12.30 release.
See QlikView WebServer: Custom HTTP Header.
You can also implement them using IIS if IIS is being used as the web server: Setting Custom HTTP Headers in IIS for QlikView.
All the best,
Sonja
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
So, if I am understanding this correctly. This setup will add a security where I won't be able to use my Qlik website or a Qlik app in an iFrame which is external to the site.
What should be done for other way around. How to mitigate the same if I want to open a link in a iFrame in my Qlik Sense Mashup?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
@Andre_Sostizzo
What should be done for other way around. Is it possible to open a link in a iFrame, in my Qlik Sense Mashup?
Currently I am getting the error
”Refused to display 'https://abc.com' in a frame because it set 'X-Frame-Options' to 'sameorigin'.”
where 'https://abc.com' is the link which I am trying to see through my qlik sense mashup using iFrame.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello @jchacko_rxsense
In order to get you the assistance that you need, I would recommend posting about your requirements and what challenges you are facing in our Integration forum.
If you, however, require direct assistance on this, our professional services are available to assist you.
All the best,
Sonja